of all websites on the internet, making it the world’s most popular content management system. WordPress security best practices However, this popularity also makes it a prime target for hackers and cybercriminals. According to recent security research, approximately 4.7 million WordPress sites fall victim to hacking attempts every year. The good news? Most of these attacks can be prevented by following proper security best practices.
WordPress Security Best Practices:
In this comprehensive guide, you’ll discover 20 essential WordPress security best practices that will help you protect your website from hackers, malware, and other security threats in 2025. Whether you’re running a personal blog, business website, or online store, these actionable steps will significantly improve your site’s security posture.

Why WordPress security best practices in 2025
Before diving into the security practices, it’s crucial to understand why WordPress security should be your top priority. A hacked website can result in lost revenue, damaged reputation, stolen customer data, and even legal consequences. According to MelaPress security survey, 41% of WordPress users still don’t use two-factor authentication, and only 30% have auto-updates enabled on their websites.
The consequences of a security breach can be devastating. Your site might be used to distribute malware, redirect visitors to malicious websites, or steal sensitive information from your customers. Google may flag your site as unsafe, causing a dramatic drop in traffic and search rankings. That’s why implementing these WordPress security best practices is not optional—it’s essential for your online success.
- Keep WordPress security best practices, Themes, and Plugins Updated
The single most important WordPress security practice is keeping everything updated. According to Patchstack research, 97% of WordPress security best practices problems are caused by outdated plugins. Software developers regularly release updates that patch security vulnerabilities, and failing to install these updates leaves your site exposed to known exploits.
Consider using WordPress maintenance tools like WPUmbrella, MainWP, or ManageWP to manage multiple sites and automate the update process. These tools save time and ensure your sites are always running the latest, most secure versions.
- Install a Comprehensive Security Plugin
A robust security plugin serves as your website’s first line of defense against threats. The best WordPress security plugins offer features like malware scanning, firewall protection, login security, and real-time threat detection.
Wordfence Security is one of the most popular options, with over 3 million active installations. It provides an endpoint firewall, malware scanner, and real-time threat intelligence. The plugin automatically scans your website for common threats and alerts you if any signs of a security breach are detected.
WordPress security best practices is another excellent choice, offering website monitoring, malware detection, and DDoS protection. One website owner reported that Sucuri blocked approximately 450,000 attacks in just three months. Other solid options include MalCare, SolidWP (formerly iThemes Security), and All-In-One WP Security & Firewall.
When choosing a security plugin, look for these essential features: malware and threat protection, access control and authentication, site integrity monitoring, backup capabilities, activity monitoring, and automatic alerts for suspicious behavior.
- Use Strong Passwords and Enable Two-Factor Authentication
Weak passwords remain one of the most common security vulnerabilities. Brute force attacks use automated bots that try thousands of username and password combinations until they find the right one. A simple password like “admin123” or “password” can be cracked in seconds.
Create strong passwords that include uppercase letters, lowercase letters, numbers, and special characters. Each password should be at least 12 characters long and unique to each platform. Avoid using easily guessable information like your name, birthday, or common words.
Two-factor authentication (2FA) adds an extra security layer by requiring a second form of verification beyond your password. WordPress security best practices This could be a one-time password (OTP) sent via SMS, email, or authentication apps like Google Authenticator. Implement 2FA using plugins like WP2FA to significantly reduce the risk of unauthorized access.
According to security surveys, 41% of WordPress users still don’t use 2FA. Don’t be part of this statistic—enable 2FA today to protect your admin accounts from brute force attacks.
- Change the Default “Admin” Username
Many WordPress sites still use the default “admin” username, making it incredibly easy for hackers to launch brute force attacks. If attackers already know your username, they only need to guess your password.
To change your username, go to Users > All Users in your WordPress dashboard. Create a new user with an Administrator role and assign it a unique, hard-to-guess username. Once you’ve created the new admin account, log out and log back in with the new credentials. Then, delete the original “admin” user.
Never use obvious usernames like “admin,” “administrator,” or your domain name. Instead, choose something unique and unrelated to your website or personal information.
- Implement a Web Application Firewall (WAF)
A Web Application Firewall (WAF) acts as a protective barrier between your website and the internet, filtering malicious traffic before it reaches your server. WordPress security best practices WAFs can block connections from known malicious IP addresses, prevent SQL injection attacks, and stop cross-site scripting (XSS) attempts.
There are two types of WAFs: application-level firewalls and website-level firewalls. Application-level firewalls inspect traffic once it reaches your server, while website-level firewalls (cloud-based) filter traffic before it even reaches your website.
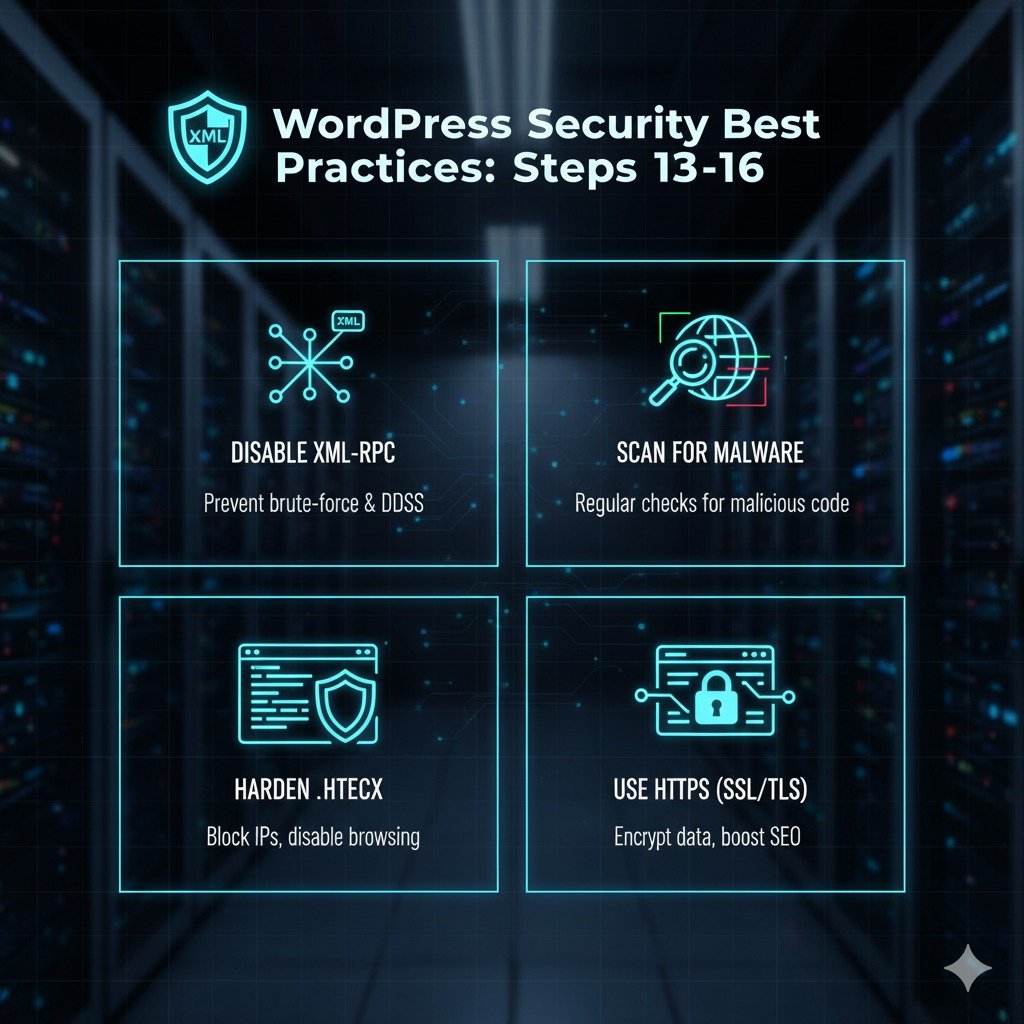
Leading security plugins like Wordfence and Sucuri include firewall functionality. Configure your firewall to filter traffic from known malicious IPs and botnets. Consider disabling XML-RPC if you’re not using it, as it’s a common attack vector.
- Limit Login Attempts
By default, WordPress allows unlimited login attempts, making your site vulnerable to brute force attacks. Limiting the number of failed login attempts dramatically reduces this risk.
Set a limit of three to five failed login attempts before temporarily blocking the user. After exceeding the limit, users should wait 15-30 minutes before trying again. WordPress security best practices This simple measure makes brute force attacks virtually impossible while causing minimal inconvenience to legitimate users.
Use plugins like Limit Login Attempts Reloaded to easily implement this security feature. The plugin tracks failed login attempts and automatically blocks suspicious IP addresses.
- Hide Your WordPress Login URL
The default WordPress login URL (yoursite.com/wp-admin or yoursite.com/wp-login.php) is well-known to hackers, making it easy to target your site. Changing this URL to something unique adds an extra layer of security through obscurity.
Use the WPS Hide Login plugin to customize your login page URL. WordPress security best practices Change it to something memorable but not obvious, such as “yoursite.com/welcome-page” or “yoursite.com/secure-access”. This simple change significantly reduces automated bot attacks targeting the default login page.
- Install an SSL Certificate (Enable HTTPS)
An SSL certificate encrypts data transmitted between your website and visitors’ browsers, protecting sensitive information like login credentials, credit card numbers, and personal data. In 2025, HTTPS is no longer optional—it’s a ranking factor for Google and a trust signal for visitors.
Most reputable hosting providers include free SSL certificates through Let’s Encrypt. Contact your hosting provider to enable SSL for your domain. Once installed, force HTTPS sitewide to ensure all pages and resources load securely. Update your internal links and notify Google Search Console of the protocol change.
Browsers now display warning messages for non-HTTPS sites, which can dramatically increase bounce rates and reduce conversions. The small padlock icon in the address bar reassures visitors that their data is secure.
- Regularly Backup Your Website
Regular backups are your safety net in case of a security breach, server failure, or accidental data loss. Without recent backups, recovering a hacked site can be extremely difficult or impossible.
Implement an automated backup strategy that creates daily or weekly backups without manual intervention. Store backups in multiple locations—never rely solely on your hosting server. Use cloud storage services like Google Drive, Dropbox, or dedicated backup services to maintain off-site copies.
Test your backups periodically to ensure they can be restored properly. A backup that doesn’t restore is worthless when you need it most. Popular backup plugins include UpdraftPlus, BackWPup, and Duplicator.
- Remove Unused Themes and Plugins
Every inactive plugin and theme on your WordPress security best practices site represents a potential security vulnerability. Hackers can exploit outdated or abandoned plugins to create backdoors into your website, even if you’re not actively using them.
Regularly audit your installed plugins and themes. Go to Plugins > Installed Plugins and Appearance > Themes to review what’s installed. Deactivate and delete anything you don’t actively use. Be especially cautious of nulled plugins—pirated premium plugins that lack security updates and often contain malicious code.
According to research, only essential plugins should remain on your site. Each additional plugin increases your attack surface and potential vulnerabilities.
- Define User Roles and Permissions Carefully
WordPress includes several built-in user roles with different permission levels: Administrator, Editor, Author, Contributor, and Subscriber. Assigning appropriate roles is crucial for security—users should only have access to the features they need to perform their tasks.
According to Patchstack, in 2023, 12.9% of WordPress security best practices issues resulted from broken access control. Never give Administrator access unless absolutely necessary. For example, guest writers should have Contributor or Author roles, not Editor or Administrator access.
Go to Users > All Users to review and adjust user roles. Remove users who no longer need access. Use plugins like User Role Editor or Members to create custom roles with specific capabilities tailored to your team’s needs.
- Disable File Editing in WordPress Dashboard
WordPress allows administrators to edit theme and plugin files directly from the dashboard. While convenient, this feature is extremely dangerous if a hacker gains admin access—they can inject malicious code directly into your site.
- Scan Your Site Regularly for Malware
Malware can remain hidden on your website for weeks or months, silently stealing data or infecting visitors. Regular malware scans help detect and remove harmful code before it causes serious damage.
Schedule weekly or monthly malware scans using security plugins like Wordfence, Sucuri SiteCheck, or MalCare. Set up email alerts to receive immediate notifications of detected threats. Many security plugins offer automated scanning that runs in the background without impacting site performance.
When downloading themes and plugins, only use WordPress security best practices reputable sources like the official WordPress repository or verified premium marketplaces. Read reviews and check the last update date before installing anything. Abandoned plugins are security risks waiting to happen.
- Disable Directory Browsing and Indexing
By default, some servers allow directory browsing, which means anyone can view a list of files in your WordPress security best practices directories. This gives hackers valuable information about your site structure and potential vulnerabilities.
Disable directory browsing by adding this line to your .htaccess file:
text
Options -Indexes
This prevents anyone from viewing your directory contents. Access your .htaccess file through FTP, cPanel File Manager, or your hosting control panel. If you can’t see the .htaccess file, enable “Show Hidden Files” in your file manager settings.

- Implement reCAPTCHA on Forms and Login Pages
reCAPTCHA verifies that users are human, WordPress security best practices not automated bots attempting to exploit your forms or login page. This extra security layer prevents brute force login attempts, spam submissions, and automated attacks.
Add reCAPTCHA to your login page, registration forms, contact forms, and comment sections. Google’s reCAPTCHA v3 works invisibly in the background, analyzing user behavior without requiring interaction. Use the Advanced Google reCAPTCHA plugin to easily implement this protection across your entire site.
- Automatically Log Out Idle Users
Inactive login sessions represent a security risk, especially if users leave their devices unattended. Attackers can hijack open sessions to gain unauthorized access to accounts.
Configure automatic logout for inactive users after a set period, typically 15-30 minutes of inactivity. WordPress security best practices This ensures that session data isn’t exposed unnecessarily. Use plugins like Idle User Logout or Inactive Logout to implement this feature with customizable timeout periods.
- Choose a Security-Focused Hosting Provider the WordPress security best practices
Your hosting provider is the foundation of your website security. A secure host protects your site at the server level, implementing firewalls, DDoS protection, malware scanning, and regular security patches.
Look for hosting providers that offer:
Daily automatic backups
Server-level firewalls and intrusion detection
Free SSL certificates
24/7 security monitoring
99.9% uptime guarantees
Malware scanning and removal
PHP and software updates
Reputable WordPress hosting providers like SiteGround, Kinsta, WP Engine, and Cloudways invest heavily in security infrastructure. Read online reviews and evaluate their reputation for handling security issues and providing customer support.
- Secure Your wp-config.php File
The wp-config.php file contains your database credentials and security keys—it’s one of the most important files to protect. WordPress security best practices Move it one directory above your WordPress root to make it inaccessible via browser.
Additionally, change your WordPress database prefix from the default “wp_” to something unique during installation or afterward. This makes SQL injection attacks more difficult. Use WordPress security plugins to generate new security keys and salts in your wp-config.php file periodically.
Set proper file permissions: wp-config.php should be set to 600 or 400, which means only the owner can read and write.
- Monitor User Activity and Enable Logging
Knowing who does what on your website WordPress security best practices is crucial for security. Activity logging tracks user actions, login attempts, file changes, and other important events.
Security plugins like Wordfence and SolidWP include activity logging features. Review logs regularly to identify suspicious behavior, unauthorized access attempts, or unusual patterns. This information is invaluable for identifying security issues before they become serious problems.
Enable notifications for critical events like failed login attempts from new IP addresses, user role changes, plugin installations, and theme modifications.
- Stay Informed About WordPress Security
WordPress security is constantly evolving as new threats emerge and best practices change. Stay informed by following reputable WordPress security blogs, WordPress security best practices subscribing to security newsletters, and monitoring vulnerability databases.
Useful resources include:
WPScan Vulnerability Database
WPBeginner Security Blog
Wordfence Threat Intelligence Blog
Sucuri Blog
WordPress Security Release Announcements
Join WordPress security communities and forums where professionals share information about emerging threats and solutions. The more you know about WordPress security, the better equipped you’ll be to protect your website.WordPress security best practices
Common WordPress security best practices in 2025
Understanding the threats you face helps you prioritize security measures:
Plugin Vulnerabilities: 97% of WordPress security issues stem from vulnerable plugins. Always update plugins promptly and remove unused ones.
Brute Force Attacks: Automated bots attempt thousands of login combinations to guess passwords. Strong passwords, 2FA, and login attempt limits prevent these attacks.
Cross-Site Scripting (XSS): In 2023, XSS attacks comprised 53.3% of new WordPress vulnerabilities. Hackers inject malicious JavaScript into your site to steal user credentials.
SQL Injection: Approximately 20% of WordPress hacks involve SQL injection, where attackers manipulate database queries to access sensitive data. WooCommerce sites are particularly vulnerable.WordPress security best practices
Cross-Site Request Forgery (CSRF): These attacks trick users into performing actions they didn’t intend. In 2023, 17% of security issues came from CSRF vulnerabilities.WordPress security best practices
DDoS Attacks: Distributed Denial of Service attacks overwhelm your server with traffic, making your site inaccessible to legitimate visitors. Quality hosting and WAF protection defend against these attacks.
What to Do If Your WordPress Site Gets Hacked
Despite your best efforts, websites can still be compromised. Here’s what to do if you discover your site has been hacked:WordPress security best practices
Step 1: Put your site in maintenance mode immediately to prevent further damage and protect visitors.
Step 2: Change all passwords—WordPress admin, hosting account, FTP, database, and associated email accounts. Use strong, unique passwords.
Step 3: Contact your hosting provider. Many offer hacked site assistance and can scan for server-level issues.
Step 4: Install a security plugin like Wordfence or Sucuri and run a complete malware scan to identify malicious files.WordPress security best practices
Step 5: If you have clean backups from before the attack, restore your site to that version. Ensure the backup doesn’t contain the malware.

Step 6: If you need expert help, consider hiring a WordPress security service. WPBeginner Pro offers hacked site repair starting at $249.WordPress security best practices